Students spend weekend as cyber sleuths, trace fictional attack
Published: Apr 20, 2023 10:00 AM
By Joe McAdory
A large-scale cyberattack targeted a water company with aims at disrupting service to thousands of customers. What was the entry and extent of the attack? Who was behind the attack and what was its purpose?
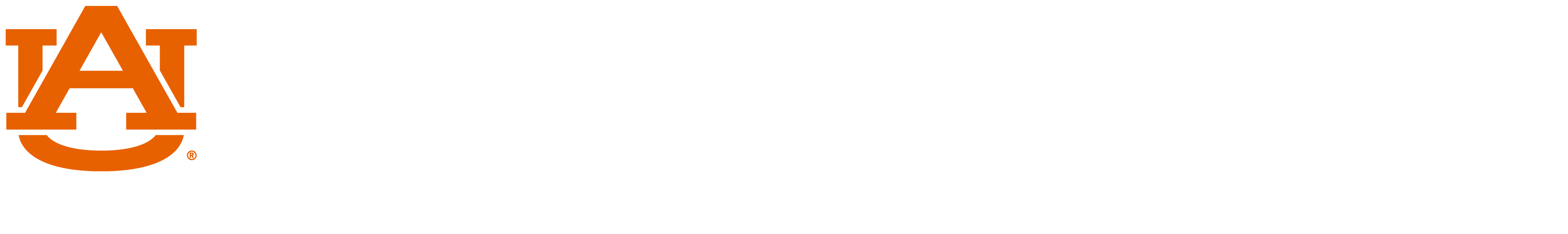
These are problems nine teams of students from Auburn University, Alabama State University, Tuskegee University, Alabama A&M University, and Columbia High School were tasked with solving at Tracer FIRE AL’23, a cyber incident response workshop & competition held April 14-16 at two sites in Alabama, one on the campus of Auburn University and the other on the campus of Alabama A&M University in Huntsville.
The Tracer FIRE educational program is developed and run by Sandia National Laboratories for the purpose of training university students in cyber incident response. Sandia develops the threat scenarios which resemble real-world attacks, and then the students at the participating universities practice investigating the scenarios with coaching by staff from Sandia’s Research and Engineering Cyber Operations and Intelligence Lab (RECOIL). The Auburn site was hosted by the Auburn Cyber Research Center and the Auburn University Ethical Hacking Club.
Sandia National Laboratories not only created the simulated attack, but also collected and packaged the forensic data into a game board with questions and puzzles for students to solve, leading them step by step through the incident response investigation. Each answered question/solved puzzle led to the next bread crumb of evidence. For instance, an employee’s computer began acting strangely after he/she opened an email. What was embedded in that email? Was this a malicious infection that spread throughout the company server where intellectual property or confidential information is at risk?

“Students are playing the role of digital detectives,” said Daniel Tauritz, associate professor in computer science and software engineering, interim director and chief cyber strategist at the Auburn Cyber Research Center, and director for national laboratory relationships. “They were familiarized with the tools of the trade, spent time learning to use these tools, analyzed data, figured out digital clues, then acquired data necessary to solve the next puzzle, and so on.”
“Students are being trained in the adversarial mindset, as they say, that is to think like your adversary. Subsequently they learn to use real-world digital forensic tools with the understanding of how the bad guys operate, how to trace them by following those breadcrumbs around the network.”
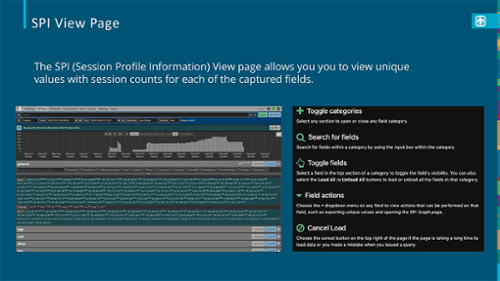
Tracer FIRE employed a plethora of open-source tools similar to those available to professionals. These tools included:
- Arkime – an indexed packet capture tool that allows analysts to search and examine the full content of network communications.
- Elastic – a popular open-source software stack that integrates three different tools – Elasticsearch, Logstash, and Kibana. This stack provides a solution for aggregating, managing, and querying log data from networked environments.
- Velociraptor – a digital forensic tool that provides endpoint monitoring of hosts on an enterprise network. This allows an analyst to closely examine the contents of files and processes running on each computer and investigate malicious software.
- Sysmon – a logging system that provides detailed information about process creations, network connections, file activity, and modifications to the system registry.
Kyle Ackerman, a junior in computer science and software engineering, was new to many cyber security software tools until Tracer FIRE.
“Before this weekend, I’ve had minimal experience with these tools, so being able to come in here and do this – in a real-world setting – is really cool,” he said. “One of the main tools we were using is called Velociraptor. I’m more of a Linux user than I am of Microsoft Windows, and being able to use the Windows tools is a completely new thing for me.”
Vicki McClendon, a senior in computer science and software engineering who looks forward to a career in cyber security, “hacking and attacking the hackers,” said, “We’ve found a lot of malicious activity on here, but we’re only looking for certain ones.”
“This weekend provided us with the opportunity to work with a variety of cyber software tools, especially logging tools,” said McLendon, who added that she continued to solve challenge problems well beyond midnight Saturday. “We revealed so many suspicious occurrences.”
Tyler Ray, a junior in computer science and software engineering and president of the Auburn University Ethical Hacking Club, said he relished the opportunity to play a role in “incident response in digital forensics.”
“I learned so much about different data forensics tools. I haven't really used a lot of these open source and online tools for investigating. I’ve learned much more about incident response, as a whole, how all the data correlates and how to look at the big picture.”
This summer, I'm going to be interning for Los Alamos National Laboratory and its Incident Response Summer School. This is really a good appetizer for getting me prepared. What happened this weekend gave me a perspective of what to expect when an attack does happen.”
Kevin Nauer, cyber security researcher and member of the technical staff at Sandia National Laboratories, oversaw the weekend event and guided students on the Auburn University site through the process; he believes real-world scenarios best prepare students for careers ahead.
“This way, when they are asked to help defend a company's network, they can kind of fall back on those experiences in these simulated events,” he said. “We discovered that out of the candidates we interview, most of the ones that are very successful and that we hire are usually ones that have participated in exercises like this. We’ve noticed that candidates who have that motivation and desire to learn more are the more successful candidates, but also the experience they get by participating in these I think always makes them more confident.”
Media Contact: , jem0040@auburn.edu, 334.844.3447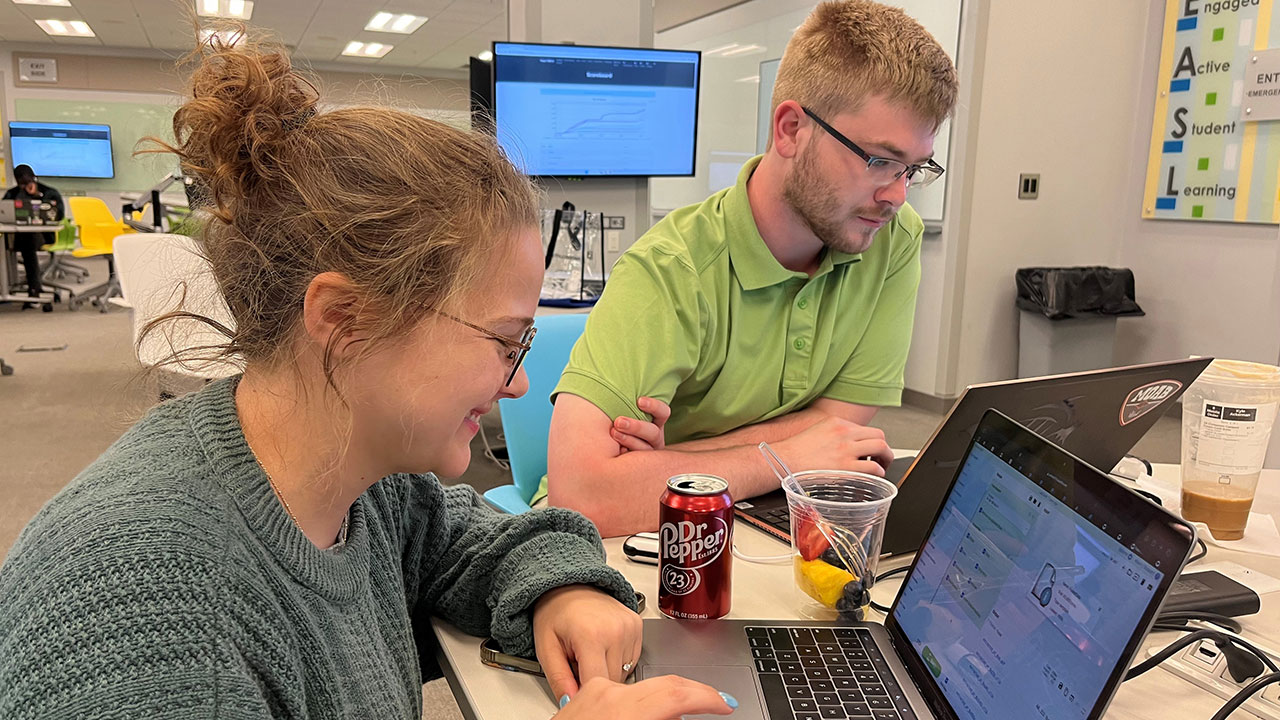
Computer science students Vicki McLendon and Kyle Ackerman enjoyed learning new software tools that trace the steps of cyber attackers.